Farahmandi Named Walden C. Rhines Endowed Professor for Hardware Security

Dr. Farimah Farahmandi, ECE Assistant Professor and Associate Director of Florida Institute for Cybersecurity (FICS) at the University of Florida, has been named as the inaugural Walden C. Rhines Endowed Professor for Hardware Security. She is the first ever Assistant Professor that has been bestowed with this distinction. The endowment will support Dr. Farahmandi’s research program, focused on hardware security verification and validation, by extending it to AI-based approaches to ensuring the security in microelectronics in pre and post fabrication stages. She is globally known for her pioneering research in the field of security verification. Her research will result in establishing security, safety, and reliability of system-on-chips (SoCs) and system-in-packages (SiPs) deployed to modern critical industrial and DoD applications.
Dr. Walden Rhines, who is continuing his father’s philosophy that “outstanding people want to work with other outstanding people,” created this endowment to support Dr. Farahmandi’s research and to support the department’s vision of growing security and trust in modern microelectronics that impacts our everyday’s life. Dr. Mark Tehranipoor, ECE Department Chair states, “Receiving such a prestigious endowment at this early part of her career, while usually this endowment is reserved for much more senior faculty in the college, speaks highly of the accomplishments made by Dr. Farahmandi. She is an innovator, leader, and outstanding collaborator to many in the college and in the community.”
Dr. Rhines is currently the President and CEO of Cornami, Inc., a fabless software/semiconductor company focused on intelligent computing for fully homomorphic encryption and machine learning. He was previously CEO of Mentor Graphics for 25 years and Chairman of the Board for 17 years. During his tenure at Mentor, revenue nearly quadrupled and market value of the company increased 10X.
Prior to joining Mentor Graphics, Dr. Rhines was Executive Vice President, Semiconductor Group, responsible for Texas Instruments’ (TI) worldwide semiconductor business. During his 21 years at TI, he was President of the Data Systems Group, held numerous semiconductor executive management positions and was directly responsible for the creation and growth of the digital signal processing business which eventually comprised about 50% of TI’s total revenue.
Dr. Rhines holds a Bachelor of Science degree in engineering from the University of Michigan, a Master of Science and Ph.D. in materials science and engineering from Stanford University, a master of Business Administration from Southern Methodist University and Honorary Doctor of Technology degrees from the University of Florida and Nottingham Trent University.Dr. Rhines grew up in Gainesville, and despite his many years elsewhere, his heart remains firmly rooted in Gainesville. Dr. Rhines’ father, Frederick Rhines, was the founder of UF’s Department of Materials Science and Engineering. His love of Gainesville is evidenced by the support which the Rhines Foundation provides the University of Florida.
FARAHMANDI RECEIVES “EXCELLENCE AWARD FOR ASSISTANT PROFESSORS in College of Engineering and University Level

At the Herbert Wertheim College Of Engineering Faculty and Staff awards luncheon held recently, Farahmandi was recognized with the honor of receiving the “Excellence Award for Assistant Professors.” Excellence Awards for Assistant Professors or is a one-time allocation in support of research. This award is conferred upon an Assistant Professor whose research performance during the year demonstrates remarkable achievement in research and other scholarly and creative activities at the highest level.
FARAHMANDI RECEIVES NSF CAREER AWARD FOR AI-ASSISTED SECURITY VERIFICATION FRAMEWORK

NSF
Career
Award
Yangbin Wang Rising Star Endowed Assistant Professor Farimah Farahmandi has received an NSF CAREER award in support of her project “SAIF: Security Assurance through AI and Formal Approaches for System-on-Chips.” The project seeks to enhance the safety and security of microelectronics by creating an innovative AI-assisted security verification framework for modern complex system-on-chip (SoC) devices.
Integrated circuits are critical components in many vital electronic devices and systems, including those used in financial services, military and defense applications, healthcare systems, and business operations. Such circuits are subject to an ever-growing number of security vulnerabilities and attacks due to their complex functionality, increased interactions among numerous functional blocks, and connectivity to the internet.
Dr. Farahmandi’s SAIF framework aims to address these vulnerabilities in a number of ways. The AI-assisted framework seeks to provide high verification coverage while dramatically reducing the time required to verify the integrity of micro devices like SOCs. By taking humans out of the process and leveraging the power of AI, the SAIF framework is able to lower security verification time by orders of magnitude while providing scalability of circuit complexity. SAIF provides computer chip design and verification engineers with properties and tools to check for security vulnerabilities before fabrication and the system promises to be extremely adaptable as new attack surfaces and modalities are discovered.
This project will integrate research and educational activities by developing a modified curriculum/syllabus for high schoolers, workforce development, minority recruiting, training/workshops for K-12 and undergraduate students, and disseminating research results through publications, seminars, tutorials, and panels.
FARAHMANDI WORKS TO OPTIMIZE CHIP LIFECYCLE MANAGEMENT
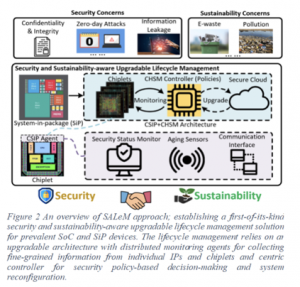
Yangbin Wang Rising Star Endowed Assistant Professor Farimah Farahmandi has received funding from the Office of Naval Research in support of her project “Optimized System Design for Assurance and Life-cycle Management (SaLEM).” The objective of the $498K project is to develop a sustainable and security-aware life-cycle management solution, called SALeM, that monitors the run-time behaviors and silicon status of microelectronic devices. The team will also develop novel designs for upgradable hardware, meaning that the design can be altered and enhanced during runtime.
SaLEM is a first-of-its-kind optimized system designed for assurance and lifecycle management. It is intended to address key sustainability and security concerns in semiconductor manufacturing while enhancing device sustainability and mitigating e-waste issues. A key feature of the SALeM system is fine-grained monitoring to enable run-time security monitoring and in-field upgrades. The monitoring is accomplished by distributed monitoring agents, essentially sensors embedded in the hardware. The monitoring agents collect and report data (e.g., aging status) from chiplets which is then transmitted to a reconfigurable fabric, an embedded FPGA (eFPGA), for further analysis. The sensors provide meticulous observability in security-critical areas, while reconfigurable hardware-based controllers offer adaptability in deploying dynamic security policies against sophisticated attacks like zero-day threats. This detailed level of data monitoring and communication will enable the recovery of systems in the field and over-the-air hardware security updates, greatly enhancing overall device security, reducing the frequency of device replacement, and enabling device reuse.
By focusing on reducing device replacement frequency, extending device lifespan, and enabling device reuse for diverse applications, SALeM aims to mitigate sustainability challenges and supply chain disruptions. The methodology shows great potential for semiconductor manufacturing, highlighting a strategy for the integration of advanced monitoring capabilities into future products.
Dr. Farahmandi’s SaLEM project continues her work in the national security space by creating trustworthy and sustainable electronics for secure and reliable hardware used in military and naval systems, the aerospace industry, financial systems, and automobile systems. Both semiconductor manufacturing companies and OEM companies stand to benefit from this research.
Silicon Design and Assurance Lab (SiLDA): A Research Incubator for Cybersecurity Testing and Assurance
Launching this month, Dr. Farahmandi’s lab, the Silicon Design and Assurance Lab (SiLDA) opened its doors for students and fellows to study and collaborate in Malachowsky Hall. This lab will serve as an incubator facilitating the development of groundbreaking, interdisciplinary work.
Housed in the new Malachowsky Hall for Data Sciences & Information Technology, the SiLDA Lab offers the latest technology and equipment designed for testing and hardware assurance.

Our Main Research Field
Over the past decades, integrated circuits (ICs) have become ubiquitous in numerous applications ranging from high-end data centers to low-power terminals. On the other hand, the security and assurance of microelectronic systems become paramount to preserve the confidentiality, integrity, and availability of sensitive data, calling for more and more research efforts from both industry and academia. At the University of Florida, the Silicon Design and Assurance Lab (SiLDA) led by Dr. Farimah Farahmandi strives to develop cutting-edge solutions for assessing security vulnerabilities of IC designs and enhancing system resilience against the most threatening attack vectors.
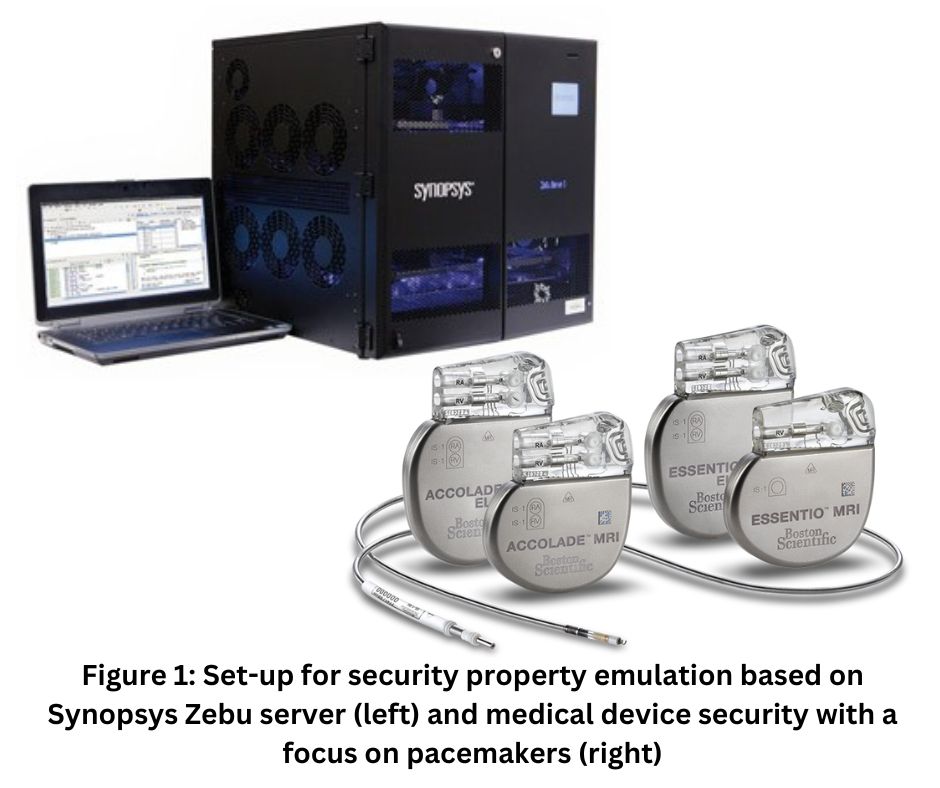
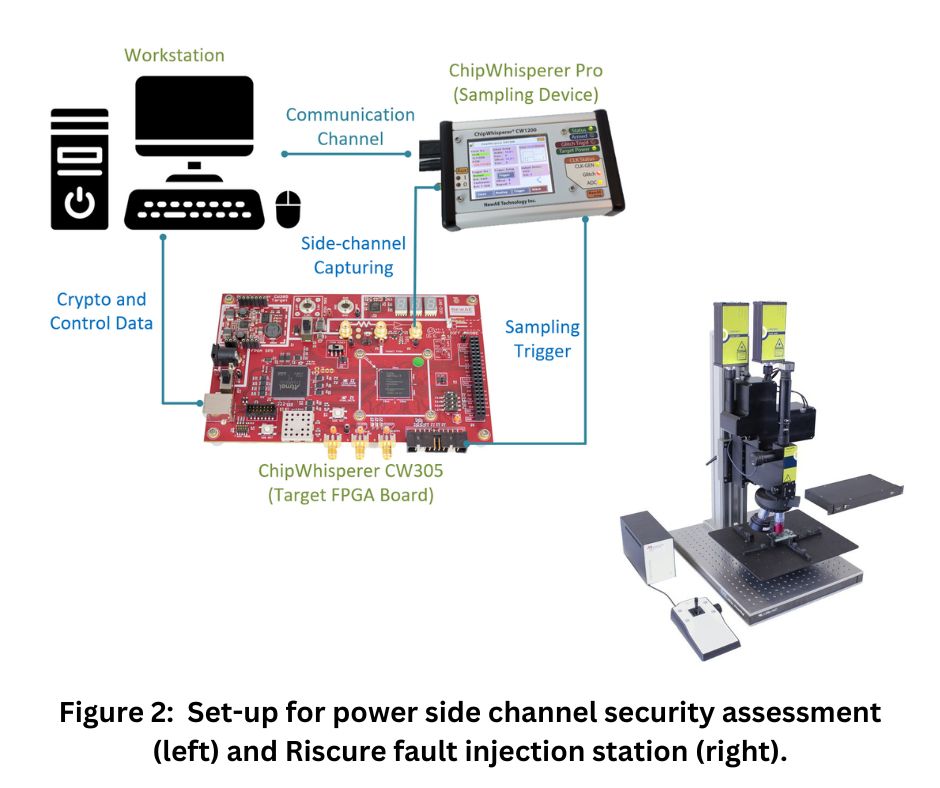
Cutting Edge EquipmentOur lab (lab 3229 in UF Malachowsky Hall) is equipped with leading security inspection instruments and experts with analysis capabilities including but not limited to (i) Security bugs emulation. For timely security closure, we have the Synopsys ZEBU emulation platform. It consists of reconfigurable devices which can accommodate the logic of the most recent processors such as Apple CPUs or Nvidia GPUs. As such, the security verification can be confirmed on real silicon while being accelerated by orders of magnitude. (ii) Medical device security. The security of medical devices greatly impacts the life safety of patients. We investigate the potential effects of physical disturbance (e.g., EM emissions from smartphones) on critical devices such as heart pacemakers. (iii) Side-channel security. Side-channel attacks can non-invasively deduce security assets from the physical properties (e.g., power, electromagnetic) of a running IC. Our lab has the pre-silicon and post-silicon platforms to prototype arbitrary cryptographic implementations for both power and EM side-channel vulnerability quantification. Specifically, our lab is equipped with quite a few ChipWhisperer instances (CW305, CW Pro, etc.) and Langer EM probing instruments (e.g., RF-K 7-4 H-field probes) for power and EM side-channel security verification, respectively.(iv) Fault injection security. Fault injection attacks can effectively compromise data and system integrity during run-time. For the security assessment of such attacks, we have a Riscue laser station to enable most fine-grained bit-flips on target devices. (v) Testing and probing for security verification.
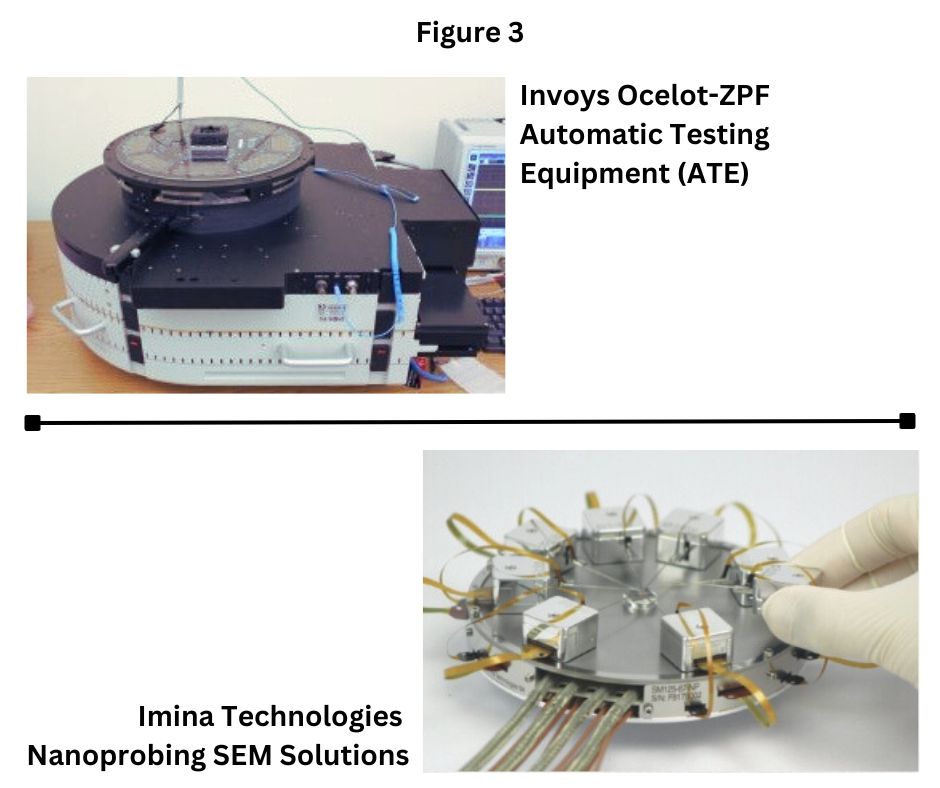
The SiLDA Lab also has the capability to identify security vulnerabilities from post-silicon (commercial-off-the-shelf) devices through testing and probing instruments. Feeding directed test vectors or directly inspecting the internals of suspected ICs using our techniques minimizes the possibility of vulnerabilities to escape.

Open House SiDA Lab: Doctoral student, Dipayan Saha, discusses Synopsis ZeBu Emulation Platform with a curious visitor. Nov. 2023
Farahmandi receives $600k grant for fault-injection research
ECE Assistant Professor Farimah Farahmandi has received funding from the Office of Naval Research (ONR) in support of her 3-year project, “FAME: Fault-Injection Assessment and Mitigation of Microelectronics at Pre-silicon.” The $600k grant supports work which aims to counter fault-injection attacks by discovering the most vulnerable locations in order to develop more efficient solutions for bolstering physical protection.
With the emergence of the Internet of Things (IoT) and edge computing that promises new and exciting applications from the military, naval, mobile, financial, transportation, and household sectors, security and privacy have emerged as major design challenges. The computing and sensing components in an IoT system, cryptographic hardware in embedded systems, reconfigurable Field Programmable Gate Arrays (FPGA) embedded systems, artificial intelligence (AI) accelerators, digital signal processors (DSPs), and microprocessors are all highly vulnerable to diverse forms of physical and non-physical attacks. These attacks appear in different forms (e.g., information leakage, side-channel leakage, fault injection, physical attacks, rowhammer) and can effectively bypass the security mechanisms built in a design, thus putting systems at risk. Among them, fault-injection attacks have become a major concern to the computer security community primarily due to their powerful capability in tampering with critical features in a device and ability to extract secrets, irrespective of the mathematical strength and robustness of the implemented security mechanisms.
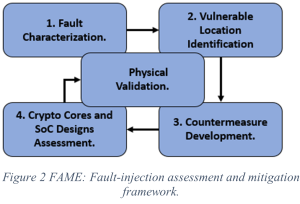
In this project, we try to detect the most vulnerable locations in a design to fault attack and place emphasis on protecting these vulnerable locations so that the countermeasure would be more efficient, and the overhead would be greatly reduced. The end goal of this project is to enable the production of hardware more resilient to various methods of fault-injection at a much more feasible cost.